where : ibrtses embedded
communication and protocols
Protocols define the way how electronic devices communicate with each other.
The seven layers of the OSI reference model cover the definition of the terms used.
a few links to the OSI-model :
Whereas most literature covers the top-down approach, here the bottom-up approach is covered.
The furter view is narrowed to embedded system developers requirements
communication hardware requirements
A communication hardware (physical layer) is selected based on the following issues :
- maximum distance
- data rate
- suszeptibility to environment
- number of devices involved
- topology, physical and logical
Based of those issues, not only the physical layer but also higher layers are influenced.
An overview over physical layer implementations for serialized data:
| type |
data rate |
distance |
#devices |
media |
| RS 232 |
up to 115k bit |
few 10m |
2 |
3 wire |
| RS 422 |
up to 1M bit |
up to 1500m |
2 |
twisted pair |
| RS 485 |
up to 1M bit |
up to 1500m |
32 (128) |
twisted pair |
| arcnet |
2.5M bit |
few 100m |
255 |
twisted pair, coax |
| ethernet |
10/100/1000M bit |
few 100m |
|
twisted pair, coax |
Notes :
the values may depend on the implementation - refer to the manufacturers datasheets.
- RS232 trades speed against distance
- RS422 & RS485 may go up to 10MBit, but there is no UART doing that.
- RS422 & RS485 may extend to 1500m or more depending on the attenuation
of the cable
- RS485 may support 128 or more devices when uPower drivers are used
- arcnet and ethernet have star topology on twisted pair and bus topology
on coax
- arcnet and ethernet have an inherent protocol
- the CAN bus is based on the RS485
- fast arcnet, fast ethernet, firewire, fibre channel are much faster and not listed
physical layer implementations
RS 232
RS 232 is implemented as 3 wire link, although several handshake lines are
also defined
and occasionally used. Supporting a device at both ends, a UART does the parallel/serial
conversion. A driver is used to generate the signal levels of +-12V
Transmission can be full duplex, up to 115kBaud
some UARTS :
- 8250 : outdated
- 16550 : as 8250 but with 16 byte FIFO
- 16552 : dual 16550
- 16554 : quad 16550
- TL16C750 : 1MBit, 64 byte FIFO
- Ox16C952 : 3MBit, 128 byte FIFO
some drivers:
- 1488 : quad transmitter, uses +12V, -12V
- 1489 : quad receiver
- DS232: 2 transmitter and 2 receiver, from 5V only
standard connectors are 9 pin and 25 pin DSUB :
| signal |
pin on DSub9 |
pin on DSUB25 |
|
| signal ground |
5 |
7 |
|
| frame ground |
? |
1 |
|
| Rx |
2 |
3 |
data in |
| Tx |
3 |
2 |
data out |
| RTS |
7 |
4 |
handshake out, connects to CTS |
| CTS |
8 |
5 |
handshake in, from RTS |
| DSR |
6 |
6 |
handshake in, from DTR |
| DTR |
4 |
20 |
handshake out, connects to DSR |
| RI |
9 |
22 |
|
| DCD |
1 |
8 |
|
The minimum requirement is signal ground, Rx and Tx.
Custom implementations may also use TTL levels or current loop.
RS 422
RS 422 is similar to RS 232, but by using different drivers, the distance
and the speed is extended. The RS 422 drivers use one twisted pair of wires
per signal. The drivers generate a differential signal.
The same UARTS as for RS 232 are used. Full duplex at up to 1MBit at distances
up to 1.5km can be achieved.
Some drivers :
- 16LS31 transmitter
- 16LS32 receiver
- ADM489 transmitter & receiver 5V
- ADM3491 transmitter & receiver 3.3V
- see also the RS485 transmitter/receiver
The minimum requirement is one pair for Tx and one pair for Rx, plus the
reference ground, as the common mode voltage is only a few volts.
RS 485
Differential drivers with tristate capability allow several devices to operate
on the same twisted pair bus. Only one device at the time may drive the bus.
This reduces the number of wires required to just one pair, inherits the great
distance and the speed known from RS 422, but the communication is half duplex now
and the protocol has to support the enabling/disabling the drivers on a message level.
When communicating with a PC, using two pairs, one for data to the PC and one for data
from the PC has the advantage of not requiring the PC to switch directions. Switching
the direction is done with the RTS. Note that the PC has problems to switch the
transmitter off after the last byte sent. As there is no interrupt when the last byte
left the UART, this event has to be fashioned with a timer. This especially applies to
a multitasking OS such WinNT. A timer of 1ms may be processed as late as 100ms, thus
crashing a tight bus timing.
There are mircopower drivers, from which more than 32 may be operated on the same bus.
The UARTs are the same as for RS 232 and RS 422.
Some drivers :
- 75176 outdated
- ADM483 250kbit
- SN65HVD23D 25MBit @ 160m
- SN65HVD24D 3MBit @ 500m
Arcnet
Arcnet is implemented on a chip such as the COM90C66 from SMC. Only a transformer to
connect to the media has to be added. The media may be coax or twisted pair.
While independant of the topology, star for twisted pair, and bus for coax, a token
is passed, the throughput of the network is sustained even with a lot of devices
communicating with each other. The token protocol also guarantees a defined response time.
Industrial realtime applications therefore favor Arcnet over Ethernet for the throughput and
the responsetime
The built-in protocol guarantees a save transmission.
Retries have to be made outside though.
There are unfortunately no drivers for WinNT
Ethernet
Ethernet is implemented on a chip such as the LAN91C96 from SMC. Only a transformer to
connect to the media has to be added. The media may be coax or twisted pair.
The underlying collision detect mechanism lets the throughput break down under heavy load.
Ethernet is favoured for PC <-> embedded system applications as there are drivers for WinNT.
On a coax, the minimal distance between two devices is 2m.
The built-in protocol guarantees a save transmission.
Retries have to be made outside though.
other physical layer considerations
issues:
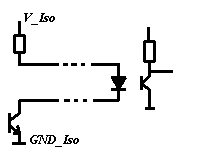
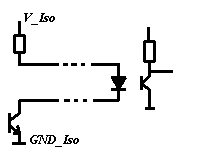
- optically isolated RS xxx
Frequently the physcal layer of RS xxx has to be optically isolated to reduce
environmental suszeptibilty. When the standard RS xxx drivers are used, a separate
supply delivers the power to the drivers at the other side of opto couplers.
A cheap RS 232 solution uses current loop

- synchronous or asynchronous
Synchronous links require the clock to be transmitted, and are primarily
used for short distance links(< 30 cm) when no UART is used. The rising or
falling clock latches the data bit
Datalink layer
The data link layer covers the access to the physical layer, detection and notification
of errors. Common is the use of a Checksum or a CRC.
- checksum
A checksum can be sum of the whole or part of the data modulo 256,
meaning the calculation is done in 8bit without overflow considerations
Or the whole or part of the message is XOR'ed to give a single byte
Checksums are simple to implement, but can only detect single bit errors
- CRC
A CRC is better, but more complex to implement and to calculate
A 16 bit CRC can protect up to 2^16bit = 8kbyte data against 2 bit errors.
For longer messages the CRC-32 is appropriate.
- parity
Parity counts the number of 1 bits and can be done by the UART. It seems
not to be used often
Short links, especially in an office or laboratory usually do not implement error detection
mechanisms, as there is no obvious cause for errors or it is recognized and can be corrected
Network layer
The network layer is used when routing of packets has to be done.
Be that multiple devices are on a bus, or multiple logical connections are on one link
Here a destination and source field are added to the message
Transport layer
This layer provides methods of flow control, ordering of received data, and
acknowledgement of correctly received data. When the devices are state machines
where a message changes the state of sender and/or receiever, the messages are
acknowledged
Session layer
This layer establishes connections or 'conversations' between processes over the network.
Here a message can be longer than the restricted length of messages of the layers below
Transmitting of large data arrays in the form of multiple messages are done here.
Presentation layer
This layer is involved in formatting data for the purpose of display or printing.
Data encryption and character set translation such as ASCII <--> EBCDIC are also
performed by protocols at this layer.
Implementing a protocol
Once the physical layer is sorted out, other issues have to be solved :
Master-Slave vs. equal priority nodes
The requirements may determine the prefered implementation :
| |
advantages |
disadvantages |
| Master-Slave |
- polled operation
- each transaction is initiated by the master
- simple to implement
|
|
| equal priority nodes |
- low latency
- high throughput
- allows event based processing
|
- collision has to be detected / avoided
- the slowest node limits the latency
- difficult to implement
|
If possible, the Master-Slave approach is prefered.
The implementation of a token protocol for the equal priority node approach has
some tricky aspects :
When a node is suddenly offline, the token has to be regenerated. How are the
ID's dynamically assigned ?
The nodes have to keep track of the messages, they have to follow a strict timing.
Protected communication
Under the following conditions, the messages have to be protected :
- long lines and/or noisy environment
- either the sender and/or the receiver of a message are state machines
the message itself can be protecteed with a checksum or a CRC.
The transaction can be protected by Ack/Nack
What happens when a CRC error is detected ? What happens when Ack/Nack is missing ?
If a statemachine is part of the communication and a part of the transaction
is missing, there must be a timeout leading to a fallback state.
Statemachines or stateless machines
Statemachines have a memory, whereas stateless machines do not have a memory.
Consider an XY plotter, which has incremental encoders for cost reasons. When
the power fails, the position is lost, it has to move to the upper left until
a sensor tells it where (0,0) is.
Consider an XY plotter with absolute encoders. It always knows the position
and can proceed where it stopped.
It may not only be that the power fails, but a bit was reversed in the communication.
How is a statemachine resynchronized ? From a known state on it has to be fed to
the current state again.
In a statemachine, every transient state has to be protected with a timeout,
then the statemachine will fall back to a known state.
Even a protocol driver is a statemachine. Consider the driver is counting bytes
till the end of the message. The sender is switched off. The driver still waits
for the remaining bytes to come. They may come as part of a new message a day later.
Unless there is a timer resetting the driver, the data received will be invalid.
Message based or streaming protocol
Streaming applications such as telephony or video may not be susceptible to
a missing frame, whereas a backup operation is.
Polled or eventbased protocol
Depending on the application, the messages can be derived from a polled operation
or from events. Depending on the requirements, either of them may make more sense.
At a given busbandwidth, how long does it take for an event to be processed
(latency), and how long does it take to have all data together ?
Do different devices have to send multiple messages to different devices ?
considerations
Here only the RS xxx physical layer is considered, as arcnet and ethernet
cover up to the transport layer
- messages more than one byte in length require a header, unless there is
sufficient bandwidth
and the timing can be used to group bytes together
- messages with non-predefined length have a length field to
ease the driver
- when signal noise may be a problem, a checksum or CRC is added
to provide message integrity
- when multiple devices are on the network, a destination- and
a source field are added
- when multiple logical connections are on the same link,
a task- or processnumber are added
- when the devices are state machines, the messages have to be acknowledged
and a timer provides a fallback to a default state
- with multidevice systems, the access to bus has to be defined,
either as master-slave, where the master initiates all transmissions,
or with equal right nodes, where either a token is passed or a collision
detection algorithm is implemented
Unfortunate choices
Maximum code
The reliability of a protocol can be improved when the header bytes are excluded
in rest of the message. In a binary protocol that is solved by excluding combinations.
Be the header [STX=0x02][length] ... and the length is never zero, then one approach may be
to add a 0x00 for every 0x02 found later on.
The point is at what level that happens.
Are the added 0x00 also counted in the [length] field ? Y/N
Are they also used for the CRC ? Y/N
There is at least one unfortunate combination, I leave it to the reader, that
leads to maximum code, with a maximum number of ifs.
And there is another combination that minimizes them.
Keep in mind that on a PC the maximal code variant is just a few lines more,
whereas on an embedded cpu, code might be valuable.
Questions ?
Suggestions?
Feedback ?
to be continued ...
sponsored links
embedded pages
home
last update: 22.dec.06 or perhaps later
Copyright (99,2006) Ing.Büro R.Tschaggelar